Firewall For IoT Devices: The Ultimate Guide
There are growing concerns over the security of IoT devices as their adoption continues to rise. These smart devices are susceptible to cyber-attacks, making them an attractive target for hackers. An intrusion of privacy or disruption of critical infrastructure can be severe consequences of a security breach.
Due to these risks, creating a firewall for your WLAN(Wireless Local Area Network) or VLAN(Virtual Local Area Network) becomes essential. A firewall is a network security device or software that acts as a barrier between a trusted internal network (such as a LAN) and an untrusted external network (such as the Internet). By monitoring and controlling incoming and outgoing network traffic based on predefined rules, firewalls aim to protect network security from unauthorized access, cyberattacks, and data breaches.
Types of Firewalls for IoT Devices
Firewalls for IoT devices come in different forms, and each of them has its advantages and applications. Here are some of them.
Network Firewalls
As the most widely used type of firewall, network firewalls are placed between the devices and the Internet, monitoring all incoming and outgoing traffic. Typical forms of network firewalls include hardware appliances, such as routers or other dedicated firewall devices.
Host-Based Firewalls
Installed directly on individual IoT devices, host-based firewalls can be considered a complement to network firewalls. They mainly monitor the local traffic of IoT devices to prevent unauthorized access.
Next-Generation Firewalls (NGFW)
NGFWs use a multilayered approach to integrate enterprise firewall capabilities with IPS and application control. As a future-oriented software, this type of firewall combines traditional firewall capabilities with advanced security features such as intrusion prevention, deep packet inspection, and application awareness. This type of firewall is also known as Unified Threat Management (UTM) or Cloud Firewall.
IPS: Abbreviation for Intrusion Prevention System, is a technology that monitors a network for any malicious activities attempting to exploit known vulnerabilities.
Set Up IoT Firewall Rules: Key Components to Consider
Firewall rules are essential for network firewalls since these rules define a set of instructions and configurations on a firewall to control the flow of network traffic. Here are some critical components of network firewall rules.
- Traffic Direction: Traffic direction refers to network data flow allowed or blocked by the firewall's rule set. Network traffic has two main directions: inbound traffic (incoming from external sources to the internal network) or outbound traffic (outgoing from the internal network to external destinations).
- Source and Destination: Source refers to the origin of the traffic, such as an IP address, network range, or domain. Destination denotes the intended recipient of the traffic, which could be a specific IP address, port, or service.
- Protocol and Ports: Communication protocol and specific ports are associated with the allowed or blocked traffic. Standard protocols include TCP (Transmission Control Protocol) and UDP (User Datagram Protocol). Ports represent communication endpoints through which services or applications operate.
- Action: Actions determine what to do with the matching traffic. The two primary actions are "Allow" and "Deny" (or "Block"). An "Allow" action permits the traffic to pass through the firewall, while a "Deny" action blocks the traffic from proceeding.
- Rule Order and Priority: Firewall rules are evaluated sequentially, and the order matters. When a packet matches multiple rules, the firewall applies the first matching rule in the sequence. You can set rule priorities to control the rule evaluation order explicitly.
- Logging: Logging options are also crucial for firewall rules. When logging is enabled, the firewall records information about the traffic that matches the rule, such as source IP, destination IP, and timestamp.
- Statefulness: Statefulness means that firewalls can keep track of the state of active connections. Stateful firewalls can identify whether an incoming packet is part of an established session or a new connection attempt.
If you want to set up your firewall rules, here is a video with detailed instructions.
Resource: Youtube Tech Tutorials - David McKone
How to Access IoT Devices Behind Firewall
Although firewalls add an extra layer of protection to your home IoT devices, there are occasions when you still need to access these devices behind this barrier. Check out some standard methods to access IoT devices behind.
Port Forwarding
As a networking technique, port forwarding allows incoming internet traffic from a specific port on the router's public IP address to a particular port on a device or server within the private local network.
To use this method, you need to configure the firewall to forward specific ports from the external Internet to the internal IP address of the IoT device. You can access the IoT device from outside the local network using the public IP address and port number.
Port: A port is a communication endpoint and is usually identified as a port number associated with an IP address.
VPN
VPN, the abbreviation of Virtual Private Network, is a technology that creates a secure and encrypted connection over the Internet, which allows users to access the Internet or other resources as if they were directly connected to a private network. When using VPN to access IoT devices, choose a reputable VPN service that prioritizes your privacy and security.
SSH
SSH (Secure Shell) is a network tool that helps you securely control and handle remote devices or servers over the Internet. It establishes a safe, encrypted connection between your local computer (the client) and the remote server (a distant device or server). With the help of SSH, you can control your IoT devices remotely. Meanwhile, your sensitive data stays protected from potential eavesdroppers or hackers.
Cloud Services
If your IoT devices connect to the cloud server, you can control and access them through a smartphone app or web interface provided by the manufacturer. Most IoT services are cloud-based, making it easier for users to store necessary data.
Reverse Proxy
A reverse proxy is a server or network device that intermediates between clients (web browsers or users) and backend servers. A regular proxy forwards requests from clients to the Internet, while a reverse proxy receives requests from clients and then forwards them to the appropriate backend server on behalf of the clients. When applied to IoT devices, the operational process of this particular server is as follows: upon receiving external requests, reverse proxy servers efficiently direct them to suitable IoT devices.
Why Do IoT Devices Need Firewalls?
IoT devices require firewalls because they are susceptible to various vulnerabilities due to their unique characteristics and the challenges they face in terms of security. Some common vulnerabilities of IoT devices include the following ones.
Inadequate Authentication
Many IoT devices come with default or weak login credentials, making them easy targets for attackers to gain unauthorized access. For example, many IoT devices use default usernames and passwords. Furthermore, some devices need proper authorization mechanisms, making unauthorized users manipulate or control them quickly.
Outdated Firmware and Software
In many cases, manufacturers may not provide timely updates and security patches for IoT devices, leaving these devices vulnerable to known exploits and malware attacks. Moreover, many IoT devices lack an automated update mechanism. As a result, many users must be made aware of the importance of regularly updating their devices' firmware.
Insecure Communication
The communication between IoT devices is also vulnerable. Some IoT devices may transmit data over unencrypted channels, allowing attackers to intercept sensitive information, such as user credentials or sensor data. Lack of reliable communication can also lead to man-in-the-middle attacks.
Lack of Standardization
The current market has a wide array of IoT devices, each with its brand and manufacturer. This wide variety caters to the diverse demands of consumers, providing them with numerous options. Despite this abundance, security concerns have also emerged as a significant issue. Each manufacturer might implement security measures differently or, in some cases, not at all. This inconsistency creates a patchwork of security standards, leaving gaps that attackers can exploit.
Benefits of Using Firewalls for IoT Devices
Firewalls offer several essential benefits for IoT devices, enhance their security and protect them from potential threats. Here are some benefits of setting up firewalls for IoT devices.
Enhanced Network Security
Firewalls act as a protective barrier between IoT devices and the Internet since they can monitor incoming and outgoing network traffic. This capability can effectively prevent unauthorized access and potential cyberattacks, thus safeguarding sensitive data and device functionalities.
Reliable Access Control
Firewalls allow network administrators to define specific rules and policies for inbound and outbound traffic. This level of access control ensures that only authorized devices or users can communicate with the IoT devices, significantly reducing the risk of unauthorized access or data breaches.
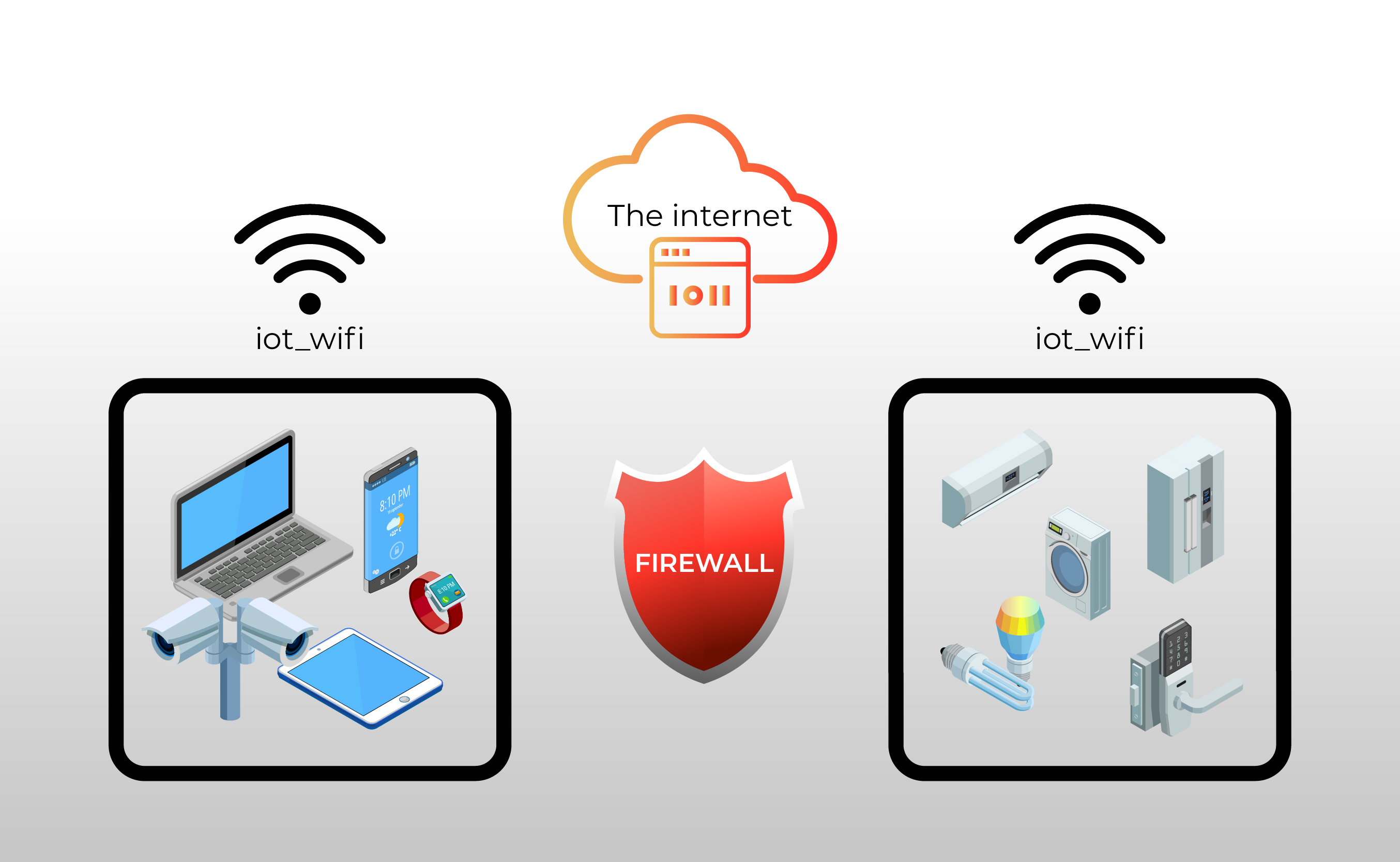
Isolation of IoT Devices
Firewalls can segment IoT devices into separate networks or VLANs (Virtual Local Area Networks), isolating them from other network parts. If a compromised device occurs, the firewall containment helps prevent the lateral spread of the attack to other network components.
DDoS Attack Prevention
Distributed Denial of Service (DDoS) attacks can overwhelm IoT devices by flooding them with excessive traffic. Firewalls with DDoS protection capabilities can mitigate these attacks, ensuring uninterrupted service and device availability.
Firmware and Patch Management
Some firewalls offer features to manage and update IoT device firmware and software patches centrally. This feature ensures that devices remain up-to-date with security improvements and vulnerability fixes.
Policy Enforcement
Firewalls allow organizations to enforce security policies consistently across all IoT devices. This enforcement can reduce the chances of configuration errors or weak security settings that might lead to potential vulnerabilities.
Bonus Tips: Best Practices for Securing IoT Devices
Securing IoT devices is crucial to safeguard your privacy, data, and the overall integrity of your networking devices. Here are some best practices to consider.
Change Credentials
Weak passwords can leave IoT devices vulnerable to hacking or unauthorized access. When setting up IoT devices, change the default usernames and passwords to unique, strong credentials. Avoid using shared or easily guessable passwords.
Update Firmware
Firmware, the embedded software that controls IoT device functionality, must be regularly updated. Without the latest firmware, devices remain susceptible to known security weaknesses, making them prime targets for hackers. Manufacturers often release updates to address vulnerabilities, so check for firmware updates and apply them promptly.
Use a Trusted Internet Connection
IoT devices heavily rely on wireless internet connectivity. Set up a strong, encrypted Wi-Fi network with a unique password. Avoid using default or easily guessable passwords for your Wi-Fi router. It is highly recommended to use WPA2 or WPA3 encryption for enhanced security.
Implement Network Segmentation
Create separate network segments or VLANs (Virtual Local Area Networks) for your IoT devices and other critical devices like computers and smartphones. This practice prevents unauthorized access to sensitive information if one device is compromised.
Disable Unused Features Timely
Regularly review the settings of your IoT devices and turn off any unnecessary features or services that have not been used for some time. This action reduces potential attack vectors and minimizes the risk of unauthorized access.
FAQs
What is the role of a firewall for IoT devices?
A firewall for IoT (Internet of Things) devices provides a protective barrier between these devices and the external network, such as the Internet or other local networks. The firewall acts as an effective security measure to control and monitor the incoming and outgoing traffic to and from IoT devices.
Are all IoT devices equally vulnerable to cyber threats?
No, not all IoT devices are equally vulnerable to cyber threats. The level of vulnerability varies depending on several factors related to security features and the deployment of each IoT device. Some essential features include security encryption, firmware updates, network configuration, etc.
How can I access IoT devices behind firewalls?
You can use several methods and techniques to access IoT devices behind firewalls. Widely-used methods include port forwarding, VPN, remote desktop or SSH, and cloud-based solutions. You can choose the proper one depending on the specific scenario and your level of control over the network.
Should I use a hardware or software firewall for my IoT devices?
The choice between hardware and software firewalls depends on your specific needs. Hardware firewalls are suitable for securing an entire network of IoT devices, while software firewalls are ideal for individual devices with limited resources.
Conclusion
The firewall serves as a crucial defense against cyber threats and a reliable protection barrier for sensitive data and the privacy of individuals and businesses. Comprehending the weaknesses of IoT devices and learning the techniques to access them behind firewalls empowers users to optimize their efficacy. Crucially, firewalls operate on fundamental rules, making each component of these rules indispensable.
Undoubtedly, the implementation of firewalls for IoT devices significantly enhances their security. We sincerely hope you find this guide beneficial. Have you configured firewalls for your IoT devices? What are your thoughts on their usefulness? Please share this article with your friends and let us know your opinions in the comments section!
Search
Subscribe for the Latest Updates
Security insights & offers right into your inbox